Embedded AI Assistant SSO Configuration - Okta OIDC
Installing Embedded AI Assistant with a Code Snippet and Okta OIDC
This method of installation allows you to embed Embedded AI Assistant on any webpage governed by Okta Single Sign-On (SSO), as long as the page supports HTML/JavaScript editing. This will create an Okta application that will allow you to copy a code snippet of the AI Assistant and paste it onto any page governed by Okta , and Embedded AI Assistant will just work, automatic authentication and all.
Prerequisite Questions
- Does the site/page you want to include Embedded AI Assistant on allow for HTML/JavaScript editing?
- If you want it to be everywhere on the site, does it support site templates, master pages, headers, footers, or other similar global page elements that support HTML/JavaScript editing?
- Is the site/page governed by Okta SSO?
- Ensure there is a tool owner with Super Admin access in your Okta instance
Installation Participants
On the day of installation, we need these individuals from your team on the call:
- Okta super admin
- Must be able to add a new application and make tenant-level configuration changes.
- Target host admin(s)
- Must be able to paste an HTML/JavaScript code snippet onto the target page or site.
Installation Overview
Moveworks can walk you through the Okta application installation on a call in about 15 minutes.
Setting up the Okta application is a one-time activity and from then on you are free to paste the code snippet onto any other site governed by your Okta OIDC at your convenience.
Moveworks will Provide the Following:
- Unique Customer AI Assistant ID
Okta App Setup Instructions
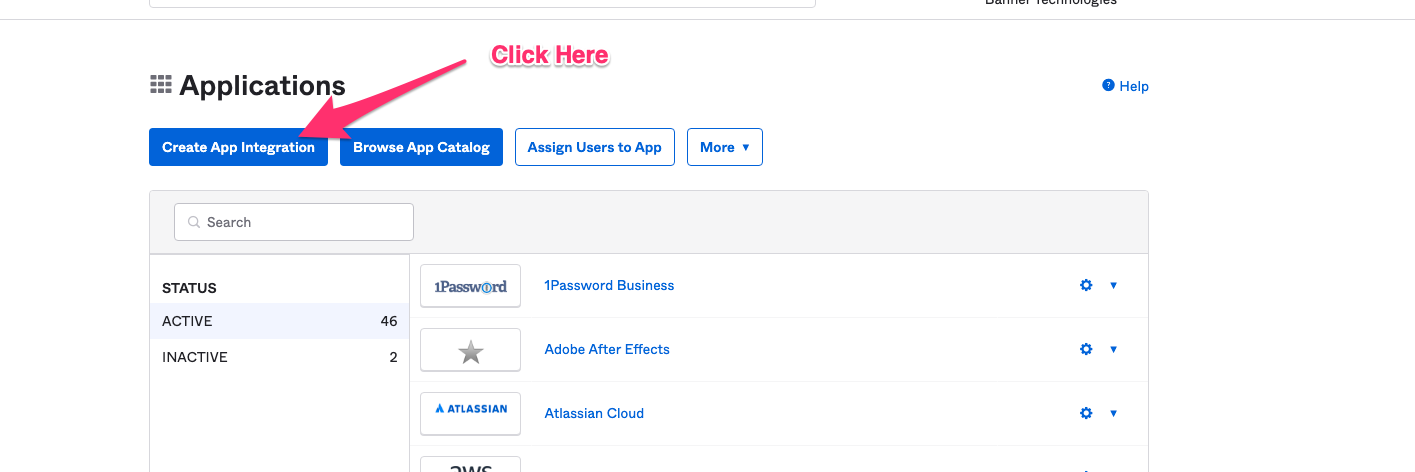
Go to the screen that lets you create Applications.
Click on Create App Integration
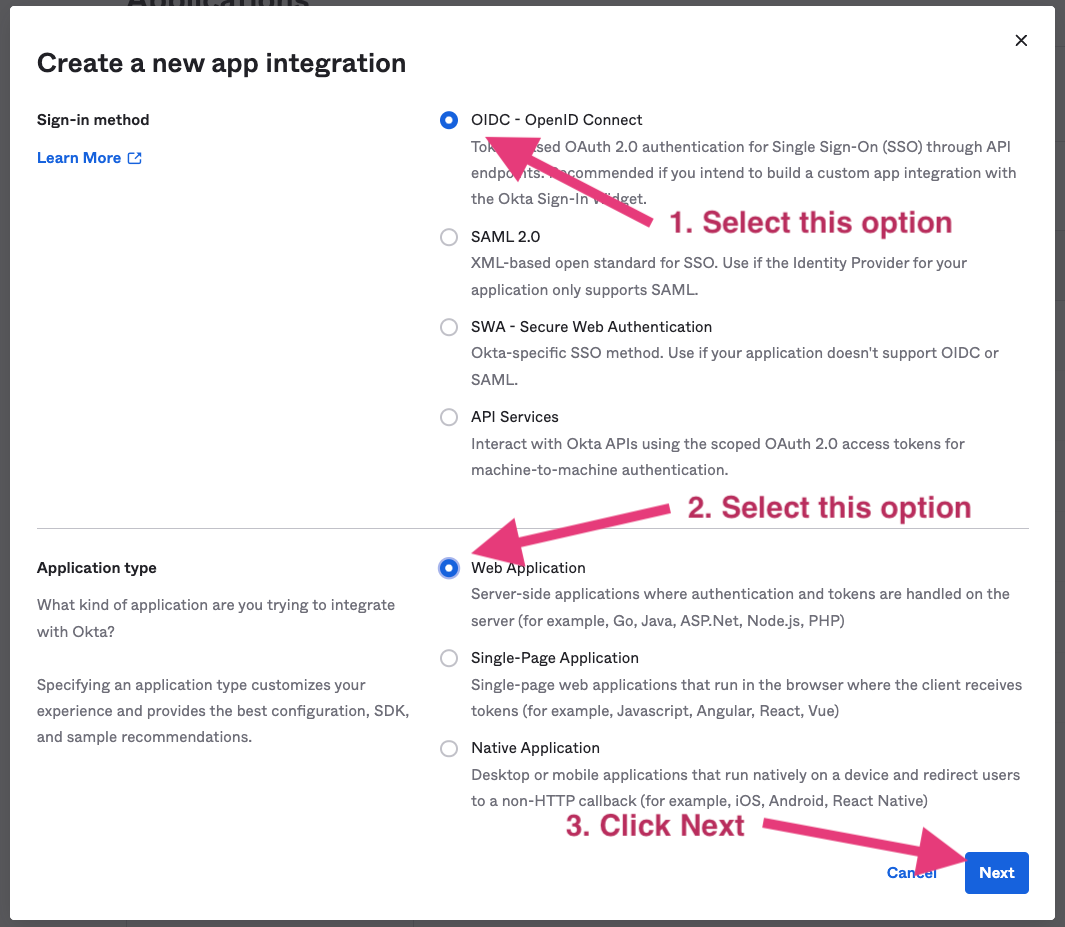
Select OIDC - OpenID Connect in the next screen.
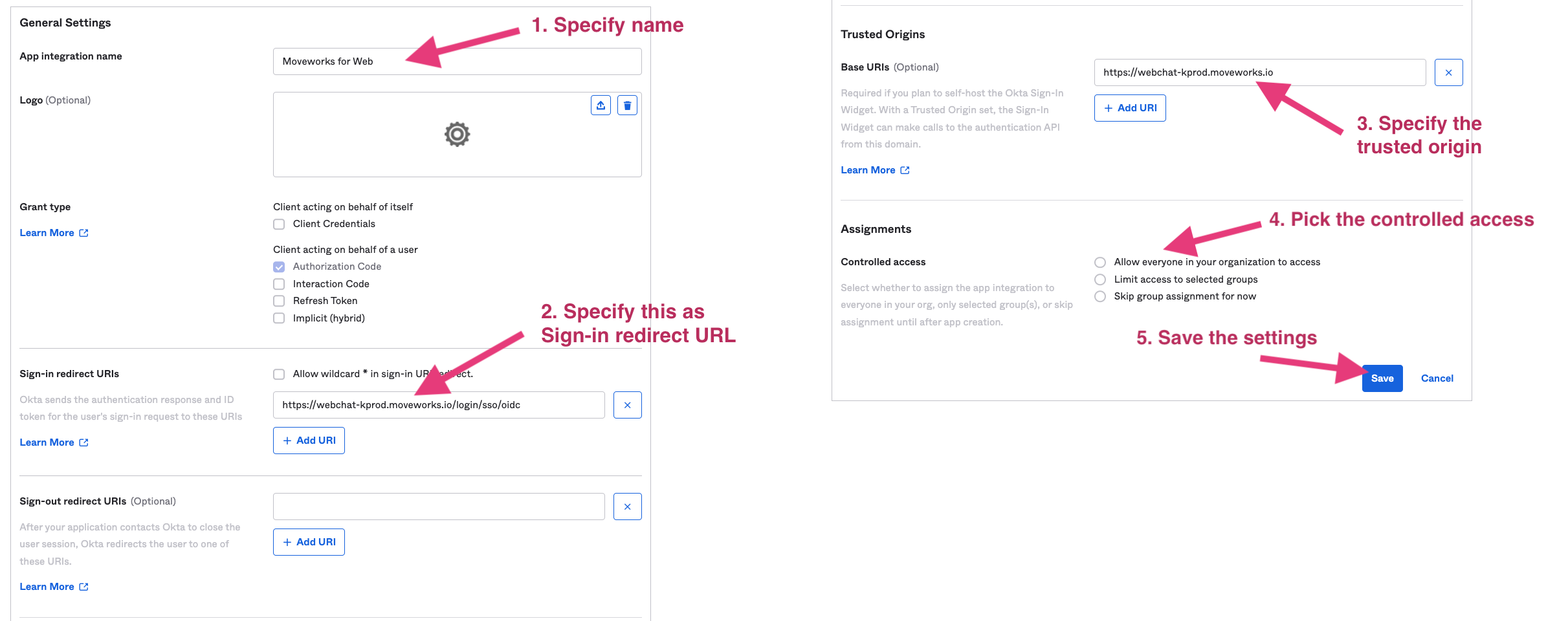
- Fill out the Settings page
- Specify a name for the application. We recommend using your bot’s name.
- Use as the Sign-in redirect URL:
Commercial Environment:
https://webchat-kprod.moveworks.io/login/sso/oidcGovCloud Environment:https://webchat.prod.am-usge1.moveworks.io/login/sso/oidcEU Environment:https://webchat.prod.am-euc1.moveworks.io/login/sso/oidcCanada Environment:https://webchat.prod.am-cac1.moveworks.io/login/sso/oidc - Specify as the Trusted Origin.
Commercial Environment:
https://webchat-kprod.moveworks.ioGovCloud Environment:https://webchat.prod.am-usge1.moveworks.ioEU Environment:https://webchat.prod.am-euc1.moveworks.ioCanada Environment:https://webchat.prod.am-cac1.moveworks.io - Configure to be one of the following options:
Allow everyone in you organization to accessLimit access to selected groups
Select options as shown below.
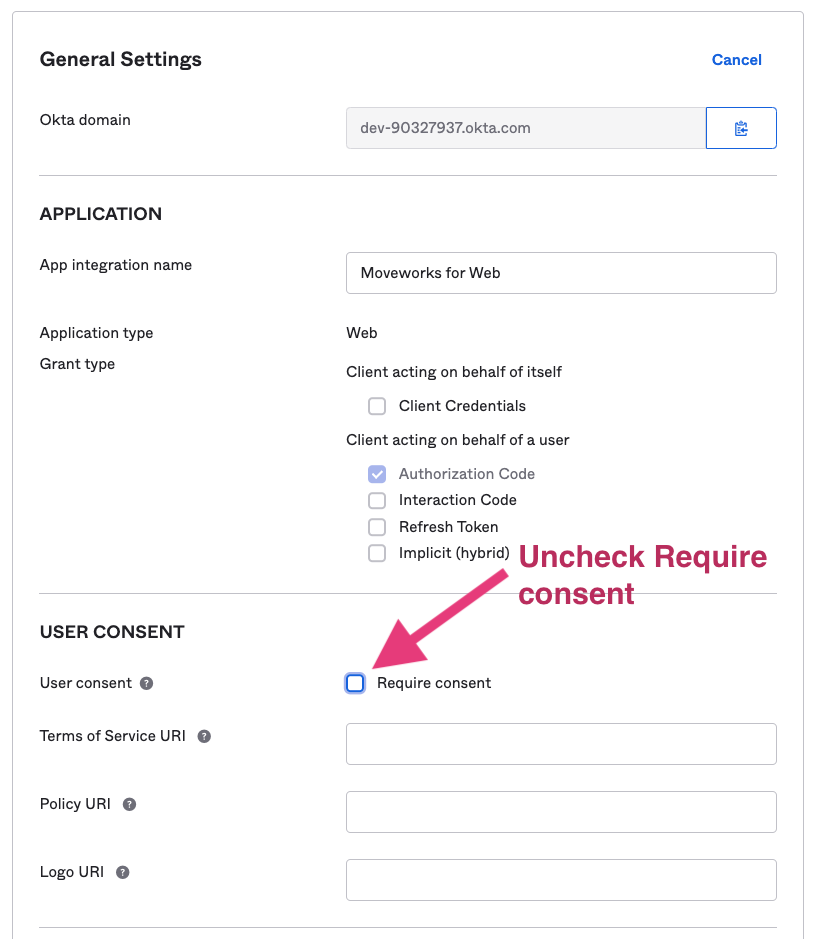
Go back to General Settings and uncheck Require consent. Since the AI Assistant is doing silent authentication, the Require consent will block the AI Assistant auth flow and leave the AI Assistant invisible.
Finish the Moveworks side of the integration
After setup is complete, login to Moveworks Setup to add the SSO application details.
- Within Moveworks Setup, navigate to Single Sign-on (SSO)
- Click create to create a new SSO configuration
- Input the following details:
- Moveworks Product: Movewebchat
- Select Connector: Okta
- Authentication Protocol: OIDC
- IDP redirect URL
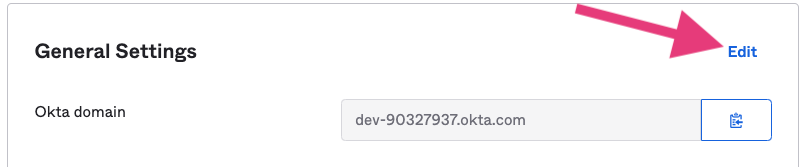
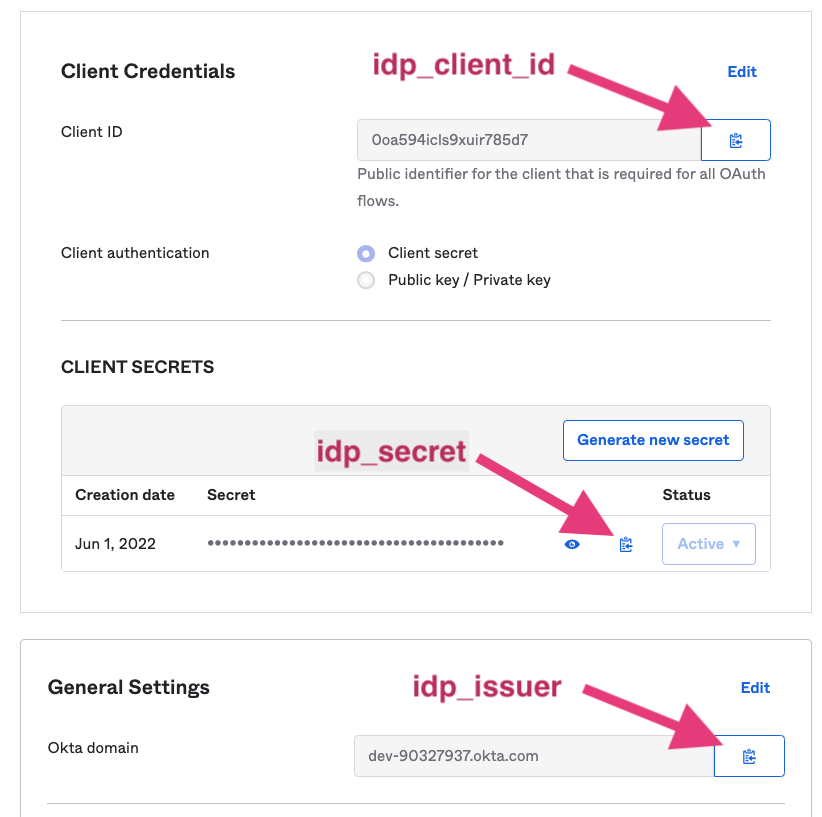
- IDP issuer: https://'okta-tenant-name'.okta.com
-
NOTE: If you are using a custom URL for your Okta login page for end users, that is the URL that must be used here, rather than the default subdomain URL.
This is because Okta session cookie is linked to the login page that is accessed. For more information, see Okta documentation here.
-
- IDP Client ID: App client ID
- IDP Client Secret: App client secret All other settings are typically not required to be populated.
- To get these information, Go to the General tab
Create Moveworks Setup Authentication Configuration
- Within Moveworks Setup, Navigate to Web Chatbot > Authentication and click create to create a new authentication record
- Set Auth Config to Generic SSO
- Set SSO Config to the SSO configuration record you created in the previous section of this guide.
- Set Auth Key to defaultfor single SSO authentication setups. For setups where you have multiple SSO systems users use to authenticate, follow the Multi SSO Configuration Guide
Configure the Embedded AI Assistant
You will need to follow the Embedded AI Assistant Configuration Guide to complete the remaining setup steps if you have not done so already.
Updated about 1 month ago