Log Data Security
Redaction Policy
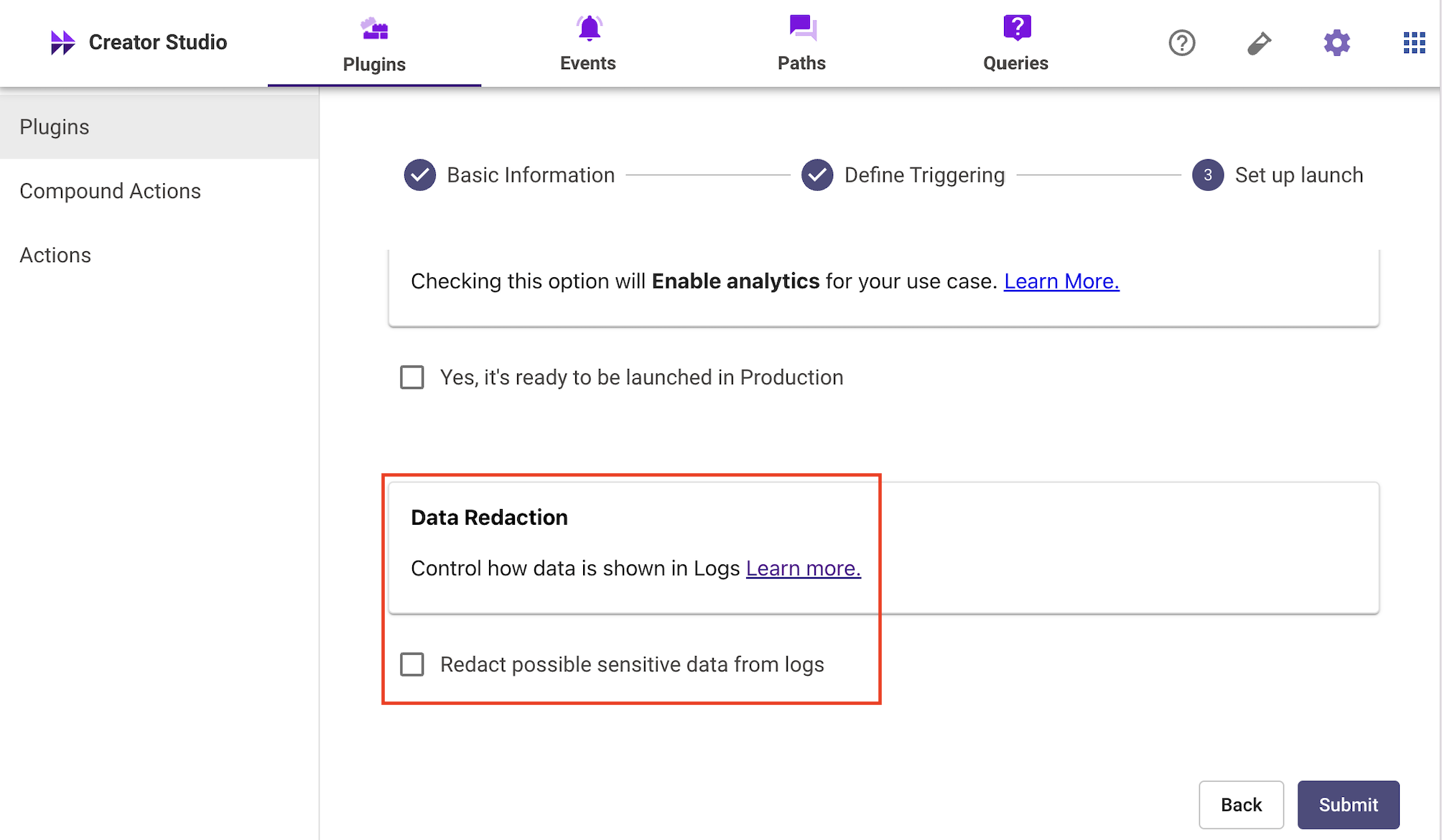
All of the logs emitted from a specific Plugin can be redacted/unredacted. You can control this toggle from the Set up launch page for a specific Plugin. When a change is made, it only affects future logs emitted; it never changes logs that already exist.
Moveworks defines redaction as permanently removing information at the source so that it can never be viewed by anyone at any point in the future.
Strict Log Redaction
Strict Log Redaction: Strict log redaction redacts all logs that touch this plugin. Only the metadata will be logged. Use this setting if you're building a plugin that interacts with sensitive data and you don't want that information to be available in the debug logs app.
- We ALWAYS redact Connector information (e.g. API Keys, Access Tokens, Passwords, etc.)
- We NEVER redact metadata coming from a log. View the full list of metadata attributes here.
- compound_action.trigger, compound_action.step,action.http logs will have PII & sensitive data redacted.
Standard Log Redaction
- We ALWAYS redact Connector information (e.g. API Keys, Access Tokens, Passwords, etc.)
- We NEVER redact metadata coming from a log. View the full list of metadata attributes here.
- compound_action.trigger, compound_action.step,action.http logs will be fully unredacted.
Redacting HTTP Actions
Moveworks redacts data being logged in your HTTP requests. When redacting, we leave the first and last character of sensitive information intact, and substitute the inner contents with a fixed number of ***** characters.
- All headers are partially redacted For example
Will be redacted as
Authorization: Bearer SECRET_TOKEN Content-Type: application/jsonAuthorization: B*****N Content-Type: a*****n - Query parameters are partially value-redacted For example
Will be redacted as
example.com/api/action?param1=value1¶m2=longerValue2example.com/api/action?param1=v*****1¶m2=l*****2 - JSON request bodies are partially value-redacted For example
Would be redacted as
{ "name": "John", "password": "secret", "info": { "email": "[email protected]", "phones": [ "123-456-7890", "987-654-3210" ] } }{ "name": "J*****n", "password": "s*****t", "info": { "email": "j*****m", "phones": [ "1*****0", "9*****0" ] } } - Non-JSON request bodies are fully redacted For example
Would be redacted as
urlencodedKeyA=valueA&urlencodedKeyB=valueB<REDACTED_NON_JSON_PAYLOAD> - The API endpoint is not redacted. You will be able to see the original base URL & the path.
Retention Policy
By default, your system logs are retained for a period of two weeks.
Updated 8 months ago